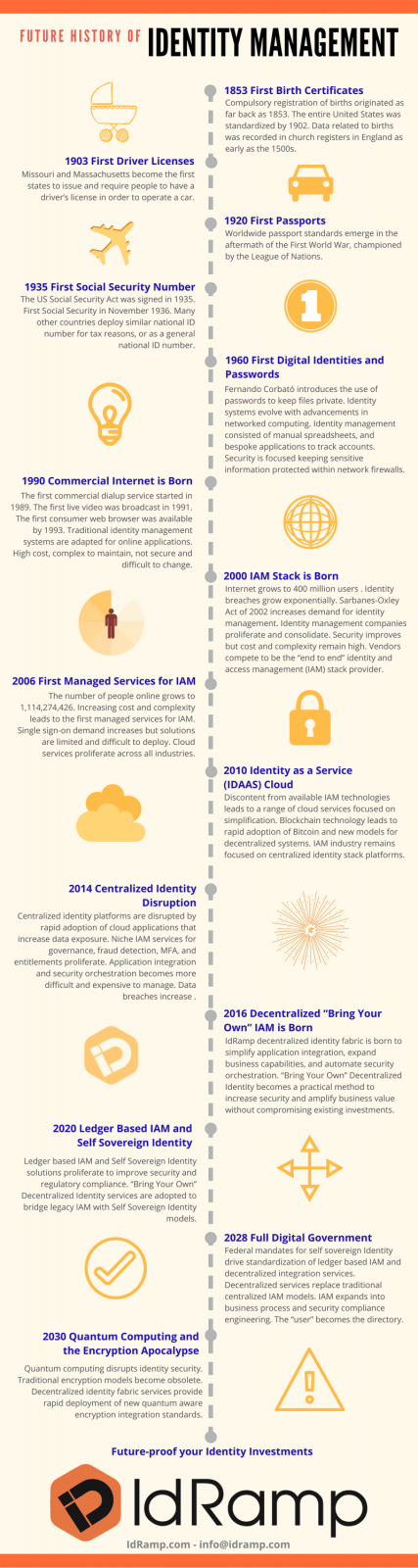
History of Identity Management Infographic
History of Identity and Access Management (text version)
1853 First Birth Certificates – Compulsory registration of births within the United Kingdom government originated as far back as 1853. The entire United States was standardized by 1902. Data related to births was recorded in church registers in England as early as the 1500s.
1903 First Driver License – Missouri and Massachusetts become the first states to issue and require people to have a driver’s license in order to operate a car.
1920 First Passports – Worldwide passport standards emerge in the aftermath of the First World War, championed by the League of Nations.
1935 First Social Security Numbers –The US Social Security Act was signed in 1935. John David Sweeney, Jr., of, New York was issued the first Social Security in November 1936. Many other countries deploy similar national ID number for tax reasons, or as a general national ID number.
1960 First Digital Identities and Passwords – Fernando Corbató introduces the use of passwords to keep individual files private. Identity management systems evolve with advancements in networked computing. Identity management consisted of manual spreadsheets, and bespoke applications to track accounts. Security is focused keeping sensitive information protected within network firewalls.
1990 Commercial Internet is Born – The first commercial dialup service started in 1989. The first live online video was broadcast in 1991. The first consumer web browser was available by 1993. Traditional identity management systems are adapted for online applications. High cost, complex to maintain, not secure, and difficult to change.
2000 Identity Management Stack is Born – Internet grows to 400 million users worldwide. Identity theft and data breaches grow exponentially. US Sarbanes-Oxley Act of 2002 increases demand for identity management due to regulatory compliance. Identity and access management companies proliferate and consolidate. Security improves but cost and complexity remain high. Vendors compete to be the “end to end” identity and access management provider.
2006 First Managed Services for Identity Management – The number of people online grows to 1,114,274,426. Increasing cost and complexity leads to the first managed services for IAM. Single sign-on demand increases but solutions are limited and difficult to deploy. Cloud services start to proliferate across all industries.
2010 Identity as a Service (IDAAS) Cloud – Demand and discontent from available IAM technologies leads to a range of IDAAS cloud services focused on simplification, automation, and reduced cost. Blockchain technology leads to rapid adoption of Bitcoin and new models for decentralized systems. The IAM industry remains focused on centralized identity stack platforms.
2014 Centralized Identity Disruption – Centralized identity platforms are disrupted by rapid adoption of cloud applications that increase data exposure. Niche IAM services for governance, fraud detection, MFA, and entitlements proliferate. Application integration and security orchestration becomes more difficult and expensive to manage. Data breaches increase rapidly.
2016 Decentralized “Bring Your Own” Identity Management is Born – IdRamp decentralized identity fabric is born to simplify application integration, expand business capabilities, and automate security orchestration. “Bring Your Own” Decentralized Identity becomes a practical method to increase security and amplify business value without compromising existing investments.
2020 Ledger Based IAM and Self Sovereign Identity – Ledger based IAM and Self Sovereign Identity solutions proliferate to improve security and regulatory compliance. “Bring Your Own” Decentralized Identity services are adopted to bridge legacy IAM with Self Sovereign Identity models.
2028 Full Digital Government – Federal mandates for self sovereign Identity drive standardization of ledger based IAM and decentralized integration services. Decentralized services replace traditional centralized IAM models. IAM expands into business process and security compliance engineering. The “user” becomes the directory.
2030 Quantum Computing and the Encryption Apocalypse – Quantum computing disrupts identity security as traditional encryption models become obsolete. Decentralized identity fabric services provide rapid deployment of new quantum aware encryption integration standards.
Now – Contact IdRamp to learn more about future-proofing your identity and access management investments.
To request a print ready version of the History of Identity Management infographic please contact IdRamp.