ID Verification Orchestration News and Resources
ID Verification for Microsoft Entra: The Human Firewall
North Korean IT workers successfully infiltrating Fortune 500 companies by using stolen identities and sophisticated deception techniques.
Identity Verification for SailPoint: Stopping Account Takeovers
All identity systems face a common challenge: what happens when legitimate users can’t log in? How do you verify users accurately?
IdRamp Attains SOC 2 Type 2 Compliance: Strengthening Security for Identity Verification Orchestration
IdRamp has successfully achieved SOC 2 Type 2 compliance, underscoring our unwavering commitment to the highest standards of security for Identity Verification Orchestration.
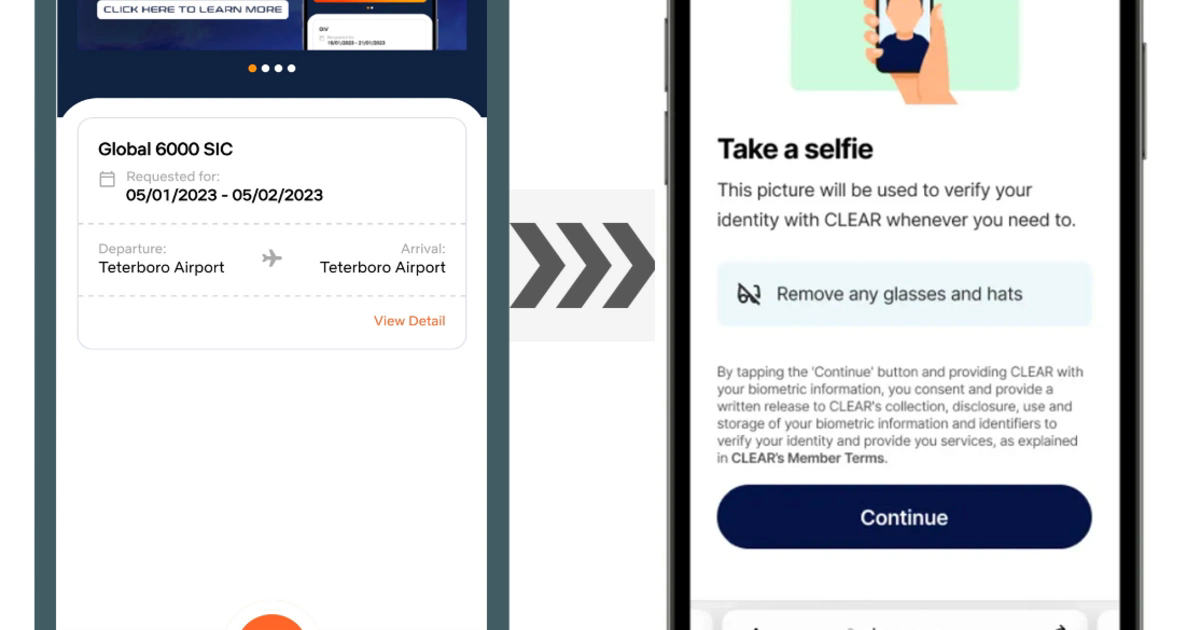
Secure Your Service Desk: ServiceNow CLEAR Identity Verification
IdRamp partners with ServiceNow and CLEAR to deliver frictionless identity verification (IDV) for your service desk workflows, strengthening security while maintaining a seamless user experience.
Account Takeover in Healthcare: How to Deliver Security and Trust
Recent warnings from the U.S. Department of Health and Human Services highlight the alarming surge in ATO incidents targeting healthcare and public health organizations
Account Takeover Attack (ATO) Defense: A Guide to Protecting Your Company
Account takeover (ATO) attacks have become a sophisticated and pervasive threat, with criminal organizations targeting businesses of all sizes and types. By gaining unauthorized access to company accounts, attackers can disrupt operations, steal sensitive data, and damage a company’s reputation.
Ping Identity Partner Profile
Ping Identity delivers intelligent identity solutions for the enterprise. We enable companies to achieve Zero Trust identity-defined security and more personalized, streamlined user experiences.
CrewBlast Partners with CLEAR and IdRamp for ID Verification
CrewBlast, an app-based air crew staffing company, has enhanced its platform by integrating advanced identity verification technology. The company said this move, in partnership with IdRamp and Clear, introduces a new standard of security and efficiency.
IdRamp: Your Gateway to CLEAR Identity Verification
In today’s complex cybersecurity landscape, robust identity verification and secure authentication are essential for safeguarding sensitive data and protecting your organization from evolving threats.
IdRamp Named Microsoft Entra Verified ID Service Partner
MS Entra Verified ID is an open standards-based solution that helps organizations protect themselves from the risk and loss of identity fraud, phishing, and credential attacks.